When Facebook announced last Friday that 50 million user accounts had been compromised, many of us weren't sure what to think.

Did that mean 50 million users had been exposed to content from a coordinated misinformation campaign, a la the 2016 U.S. presidential elections?
Or did it mean that their personal data had been improperly harvested by an app developer, as was the case for 87 million users in the Cambridge Analytica scandal?
Neither. This time, the bad actors were hackers -- and they were able to take advantage of three separate site bugs in a way that allowed them to take over user accounts, and use them as if they were the account owners themselves.
But it seems as though there's a widespread misunderstanding around what exactly happened, and just how serious the implications might be. And that's understandable -- it's a complex hack about which not a ton of information has been revealed, especially by Facebook, leading to a mixed reaction among users.
Here's what happened -- as well as what our data shows about user sentiment in light of the latest breach, and what could be behind that reaction.
A Breakdown of What Happened
Facebook first reported the breach on Friday, September 28 -- approximately three days after the full issue was allegedly first discovered, according to an official statement written by VP of Product Management Guy Rosen.
There was an usual spike in activity detected by the site around the middle of September -- the 16th, according to remarks made by Rosen during a press call -- which led to an investigation and the full discovery on the 28th.
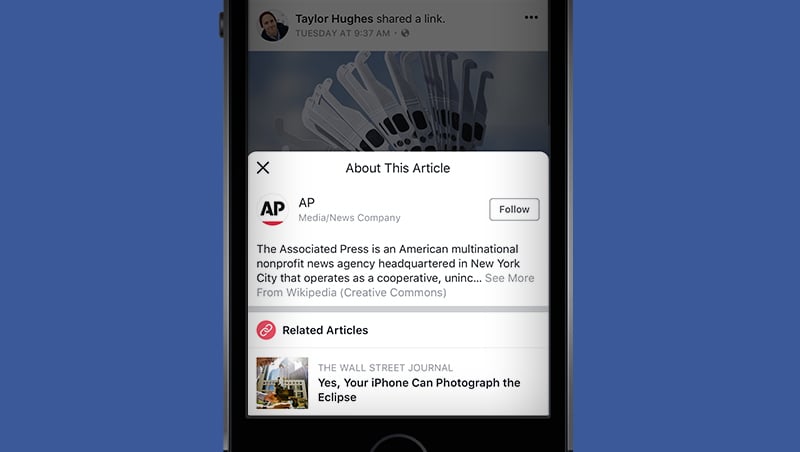
It began with a vulnerability in the site's "View As" feature, which allows users to see what their profiles might look like to another user.

Source: TechCrunch
Using the View As feature should allow you to do only that -- and when functioning properly, it blocks out any ability to enter text into compose boxes or otherwise alter the profile being viewed.
However, due to this first bug, View As provided the opportunity to upload a video.
It's because of that video uploader being displayed that the second bug occurred.
For the second bug, the video uploader improperly generated an access token.
What's an access token? Essentially, an access token allows you to use one account (like Facebook, Twitter, or Google) to log into several different services or apps.
You might be familiar with Facebook Login, which allows users to log into an app using their Facebook credentials, whether it's Facebook itself or another app using these permissions, like Tinder. The images below show what a Facebook Login looks like on Tinder.


That access token then provides the third-party app with access to the user's Facebook data -- such as the public profile, friends list, birthday, photos, Page likes, and email address indicated in the Tinder login pictured above.
HubSpot Director of Web Development Dmitry Shamis describes an access token as "a password you don't have to reenter," which allows you to stay logged into both Facebook and these other apps without having to go through the process again.
And here’s where the third bug comes in. The access tokens generated by the first and second bugs were actually for the accounts of users whose names were entered in the "View As" box, and not the user whose profile was being viewed.
As Rosen put it: the access token generated "was not for you but the person being looked up. That access token was then available in the HTML of the page, which the attackers were able to extract and exploit to log in as another user."
Therefore, the hackers could "use the account as if they are the account holder," Rosen said. The access tokens of roughly 50 million users were taken. Facebook also said that an additional 40 million users were subject to a “View As” look-up over the last year -- though it is not clear if access tokens were taken for those accounts.
Why It Might Be Worse Than It Looks
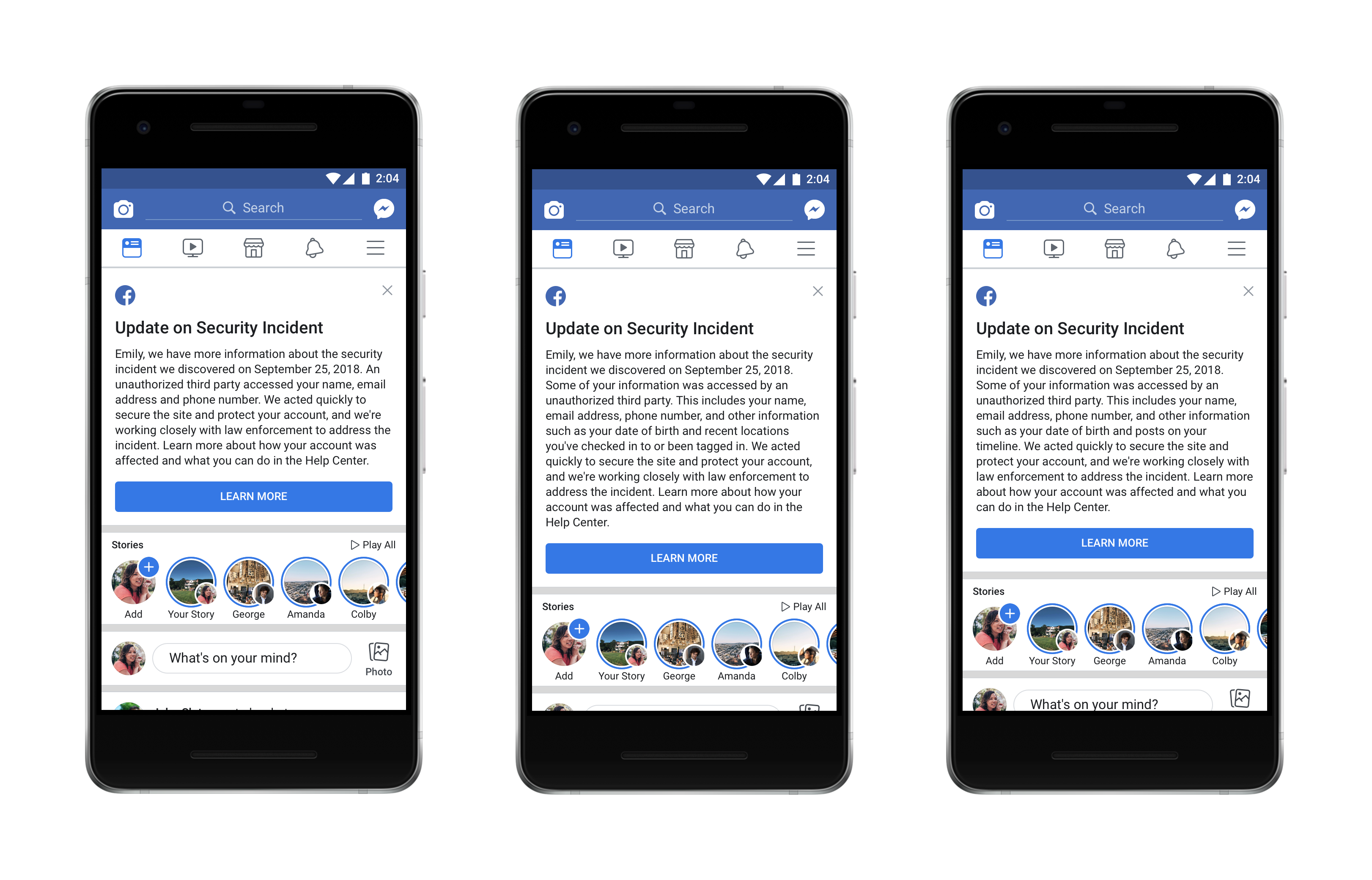
Facebook has outlined the measures it's taken in response to the breach, starting with repairing the "vulnerability," removing the View As functionality (for now), and doing a full reset of the access tokens for the 50 million accounts affected by the hack.
According to remarks made by Rosen during a press call last Friday morning, that reset made the access tokens taken by hackers "not usable anymore."
But according to Jason Polakis, an assistant professor of computer science at the University of Illinois at Chicago, that might not be the case, based on findings from a study he and others at the university conducted.
According to the study's findings, if the hackers in this Facebook breach did, in fact, gain access to third-party apps as the users whose accounts were compromised -- there are ways for them to keep that access, even if the tokens are reset, as Rosen described.
More importantly, once attackers gain access to those 3rd parties, they can maintain access to user accounts in those websites using the cookies set by those sites. No matter what FB does, they can’t do anything to prevent attackers’ from accessing those accounts. (9/n)
— jason polakis (@jpolakis) September 29, 2018
Now, Polakis was sure to specify that this phenomenon might not be "applicable here." But Facebook has said itself that it has very little information about how these access tokens were used by the hackers, and is uncertain of when the tokens were first obtained.
According to Axios, Tinder has since said it hasn't found any "evidence to suggest accounts have been accessed based on the limited information Facebook has provided" -- but at the same time, Facebook hasn't provided the app with a list of users affected by the hack. Having that information, Tinder said, would be "very helpful" in determining how the stolen access tokens may have been used on its app.
NEW: Tinder says there's no evidence accounts were *accessed* due to Facebook breach, but says Facebook hasn't shared information that would be "very helpful" to its investigation. https://t.co/EYMrv4qAwi tip @techmeme
— David McCabe (@dmccabe) October 1, 2018
Spotify, which also offers Facebook Login, also told the publication that it has not experienced a breach as a result of the hack. Facebook says that its investigation into the issue is still in its early stages.
Facebook wrote in a statement on Tuesday that an investigation and analysis of its "logs for all third-party apps installed or logged in during the attack we discovered last week ... has so far found no evidence that the attackers accessed any apps using Facebook Login." But there are still a few outstanding questions about the potential reach of the hack and impact on third-party app logins, as outlined by malware expert Jake Williams:
What Facebook isn't saying here:
— Jake Williams (@MalwareJake) October 2, 2018
1. How far back do their logs go for access token use?
2. Which 3rd party apps do and do not regularly check for token validity?
3. What would evidence of misuse of access tokens look like? What are they checking? https://t.co/BE7XhIhYCp
Public Perception: Do People Care About the Hack?
On the Monday after news of the breach first broke, we ran two surveys.
The first survey asked 727 internet users across the U.S., UK, and Canada: "Following Facebook's site hack announced last week, are you more or less likely to trust Facebook with storing your personally identifiable information?"
Nearly half of the respondents said that they're less likely to trust Facebook with their personally identifiable information.
.png?width=600&name=Following%20Facebook's%20site%20hack%20announced%20last%20week,%20are%20you%20more%20or%20less%20likely%20to%20trust%20Facebook%20with%20storing%20your%20personally%20identifiable%20information_%20(1).png)
Then, we ran a second survey, where we removed any mention of a site hack. We asked a separate audience of 753 internet users across the U.S., UK, and Canada: Over the past week, how would you measure your overall trust in Facebook?

Notice the difference in responses. This time, almost as many people who said that their trust in Facebook has decreased indicated that their trust levels in the company have stayed the same.
So what's to explain for the discrepancy?
Despite providing an option in the first survey for "I didn't hear about the site hack," I wondered how many respondents chose that answer before looking up the Facebook hack.
Was it possible that because we included the hack in the question, it prompted respondents to seek more information before answering the question? Do social media users have to be told that they should be outraged? Or is it just that people aren't really surprised, given Facebook's already tumultuous year?
If you ask HubSpot VP of Marketing Jon Dick, the answer may lie in the third answer.
"My feeling here is that people just assume that their data is constantly breached, so the Facebook news didn't even alarm people. You see that in your second results," he said. "But when we trigger people that something bad did in fact happen, we elicit more responses."
Combine that lack of alarm -- unless otherwise prompted -- with the fact that many users still rely on Facebook for a number of purposes. Monthly active user growth may have slowed, but globally, 223.4 million people are still on the site every month.
"My personal opinion is that people are making mental tradeoffs. It's a primary connection point to family members, to news, to society at large," says HubSpot VP of Marketing Meghan Keaney Anderson. "And for now, there is no viable replacement to that. The trade off I'd argue people are making is the very real value of that connection point, versus the not-yet-personally-actualized threat to privacy or security of data."
What's Next
As for what’s next, time will tell. As Facebook has said itself -- the investigation into the breach is still in its earliest stages.
That could mean that the full impact on users could be yet-to-be-determined or discovered -- and as more information is revealed, it could continue to impact the public perception of Facebook.
"I think some people are unlikely to change their behavior until they suffer an acute impact of the loss of privacy," says Keaney Anderson.
For now, what can the rest of us -- marketers included -- do to deal with and address the issue?
For her part, Keaney Anderson suggests that the main task is keeping audiences informed.
"Some of the work that could be done at this point is to educate people on what they should be watching out for as a result of this breach in data," she advises. "That could help people to calibrate their response."
We'll continue to cover the issue as more details come forward.
Wednesday, October 3, 2019, 8:50 A.M. EST: This article has been updated to include statements from Facebook on apps using Facebook Login.

![Looking Back on Facebook's Murky 2018: Here's Why Users Are Sticking Around [New Data]](https://53.fs1.hubspotusercontent-na1.net/hubfs/53/facebook-2018-user-motivation.jpg)
![Is Gamification the Key to Better Video Engagement? [New Data]](https://53.fs1.hubspotusercontent-na1.net/hubfs/53/video-gamification-data.jpg)
![The What, Where, and How of Video Consumption [New Data]](https://53.fs1.hubspotusercontent-na1.net/hubfs/53/What%20do%20you%20use%20Facebook%20for_%20%281%29.png)
![60% of People Are Sticking With Facebook, Even After the Latest Data Breach [New Data]](https://53.fs1.hubspotusercontent-na1.net/hubfs/53/facebook-data-breach-no-one-deleting.jpg)
